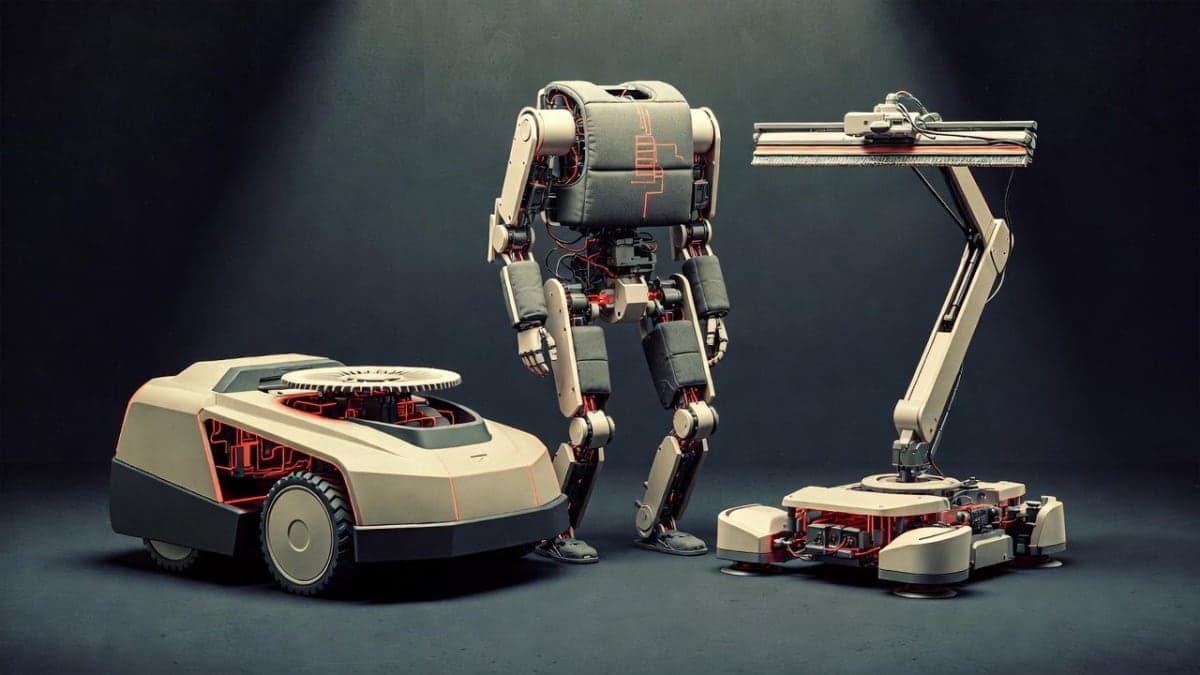
A Basque cybersecurity firm pointed an AI agent at three consumer robots and, in roughly seven cumulative hours of processing, pulled out 38 security vulnerabilities. Sixteen of them rated critical. The targets: a Hookii Neomow autonomous lawnmower, a Hypershell X powered exoskeleton, and a HOBOT S7 Pro window-cleaning robot. The tool doing the work was CAI, an open-source cybersecurity framework built by Alias Robotics and partly funded by the European Union.
The research paper, posted in early March 2026, lays out what amounts to a demolition of the consumer robotics industry's security assumptions. For years, the thinking went: hacking a physical device requires deep expertise in embedded systems and robotic middleware like ROS 2. That was the moat. An LLM-powered agent just walked across it.
The lawnmower that surveils your yard
The Hookii Neomow was the most alarming of the three. CAI started with basic network reconnaissance and immediately found an open Android Debug Bridge port on 5555, scored at CVSS 10.0. That's the maximum. Connect to it and you get unrestricted root access to the robot's Debian 11 system. No password. No prompt. Nothing.
From there the AI pulled hardcoded MQTT credentials from a config file. These credentials, the researchers found, are identical across every Hookii lawnmower ever shipped. Using them, CAI accessed the central broker server and could see 267 other robots belonging to other users. Fleet-wide control from a single set of credentials stored in plaintext.
But the data angle is worse. The Neomow broadcasts GPS coordinates every 30 seconds, generates detailed 3D maps of owners' properties via its LiDAR sensor, and captures camera images. TLS was explicitly disabled in the code (use_tls: 0). The robot also carries a 4G modem that bypasses the owner's home WiFi entirely, shipping data to AWS servers in the United States. The researchers flagged violations across multiple GDPR articles. No opt-in mechanism exists. No user consent interface. Telemetry starts the moment you power the thing on.
Someone can hijack your exoskeleton mid-hike
The Hypershell X is a consumer exoskeleton with dual motors, aimed at hikers and outdoor enthusiasts. It won a CES Innovation Award in 2025. It also has zero Bluetooth authentication.
That's not an exaggeration. CAI found that the device's BLE communications require no pairing, no PIN, no handshake of any kind. Anyone within Bluetooth range can connect and send commands. The AI discovered 177 injectable commands that control the exoskeleton's motors, including speed changes and full shutoff. On a steep mountain trail, that's not a software bug. That's a physical safety hazard.
The paper also describes an IDOR vulnerability so basic it's almost funny: to access a user's cloud data, you take the device's Bluetooth MAC address and reverse it. That's the authentication scheme. And as a bonus, CAI extracted credentials that gave access to over 3,300 internal support emails from the company's ticketing system.
What about the window robot?
The HOBOT S7 Pro accumulated 17 vulnerabilities. Same pattern: unauthenticated Bluetooth, no secure pairing. An attacker can inject motor commands, including disabling the vacuum suction that keeps the robot attached to glass. The researchers note, with characteristic understatement, that this creates a falling object hazard from elevation. The device also accepts over-the-air firmware updates without any cryptographic verification. It just installs whatever it receives.
I'll be honest, this one is less interesting technically than the other two. The Bluetooth issues are nearly identical to the Hypershell. But there's something viscerally unsettling about a robot that can be made to fall off a building via an unauthenticated wireless command.
The disclosure problem
Here's where the story gets uncomfortable for the manufacturers. According to Alias Robotics' account, the vulnerability disclosure process was largely a dead end. The researchers say they attempted responsible disclosure with all three vendors. Hookii and HOBOT reportedly did not engage. Hypershell now has a disclosure program listed on their EU website, but the researchers describe the response as inadequate, claiming the company was not accepting reports at the time of disclosure.
This is a pattern that anyone in IoT security has seen before, and it's getting old. Companies ship products with debug ports open and hardcoded passwords, then treat security researchers like nuisances when they show up with findings. The difference now is that the findings arrive faster.
Seven hours vs. the global vulnerability pipeline
The paper's broader argument is about asymmetry. CAI found 38 reportable vulnerabilities in about 7 hours of cumulative processing. The researchers estimate a human team would need roughly 33 hours for the same work. But the real bottleneck isn't discovery; it's everything downstream.
The U.S. National Vulnerability Database has been in crisis since February 2024, when NIST abruptly slowed its processing of new CVEs. VulnCheck's analysis found that 93.4% of newly reported vulnerabilities went unanalyzed between February and May 2024. The backlog swelled past 18,000 entries. NIST hired contractors, made partial progress, but as of early 2025 acknowledged the backlog was still growing, with CVE submissions up 32% year-over-year.
Then in April 2025, the CVE program itself nearly went dark. MITRE warned that its contract with DHS to operate the program was expiring. CISA stepped in with an 11-month extension at the last minute, but the episode exposed how fragile the entire vulnerability tracking infrastructure really is.
So the math is grim: AI tools can now surface dozens of flaws in an afternoon. The system meant to catalog and distribute that information can't keep up with human-speed discovery, let alone machine-speed. And manufacturers aren't patching.
The conflict of interest question
One thing the coverage of this research tends to skip: Alias Robotics is selling CAI Pro subscriptions at €350 per month. The company also sells robot security assessments, a Robot Immune System product, and defensive consulting. Víctor Mayoral-Vilches, the founder, is the lead author on the paper. The research is real and the vulnerabilities are documented, but the framing (the global cybersecurity ecosystem is collapsing, only AI-native defense can save us, here's our product) deserves the same scrutiny you'd give any vendor-funded study.
The open-source version of CAI exists and is functional. The vulnerabilities are reproducible. I'm not questioning the findings. But when someone tells you the house is on fire and also sells fire extinguishers, you note the commercial interest.
The EU Cyber Resilience Act, expected to be enforced starting in 2027, will require manufacturers to handle vulnerability disclosures and issue security patches throughout a product's lifecycle. Whether that actually changes behavior for companies shipping consumer robots from China with hardcoded credentials remains to be seen. The Hookii Neomow's open debug port isn't a subtle architectural flaw. It's a door left wide open. No regulation was needed to know that was wrong.